Every security and compliance manager knows the pressure of answering complex security questionnaires for clients across North American, European, and Asian markets. The need to prove strong, up-to-date security controls isn’t just time-consuming—it quickly turns into a productivity drain without the right tools. By focusing on efficient security questionnaire automation, your team can transform hours of manual work into a smooth, accurate process backed by evidence from your existing systems, ensuring trust and compliance without overwhelming your resources.
Table of Contents
- Defining Information Security Tools And Their Role
- Popular Tool Types And Key Capabilities Compared
- AI Automation In Security Questionnaire Management
- Integrating Tools With Compliance Workflows
- Mitigating Risks And Avoiding Common Pitfalls
Key Takeaways
Defining Information Security Tools and Their Role
Information security tools form the backbone of modern cybersecurity strategies. They’re not just nice-to-have additions to your IT infrastructure—they’re critical controls that protect your organization’s most valuable asset: data.
What Are Information Security Tools?
Information security tools are technology solutions designed to protect data from unauthorized access, disclosure, disruption, or destruction. These tools enforce security policies across your organization and ensure compliance with regulatory requirements.
Think of them as multiple layers of defense. Each tool serves a specific purpose in your overall security architecture, working together to create a comprehensive protection strategy.
Core Categories of Security Tools
Most organizations deploy several types of tools:
- Detection and prevention systems catch threats before they reach critical systems
- Encryption tools protect data confidentiality both in transit and at rest
- Access control systems ensure only authorized personnel access sensitive information
- Monitoring and logging solutions track activities for auditing and threat detection
- Vulnerability assessment tools identify weaknesses before attackers exploit them
Here’s how the core categories of security tools differ in focus and business value:
Why Security Tools Matter for Your Organization
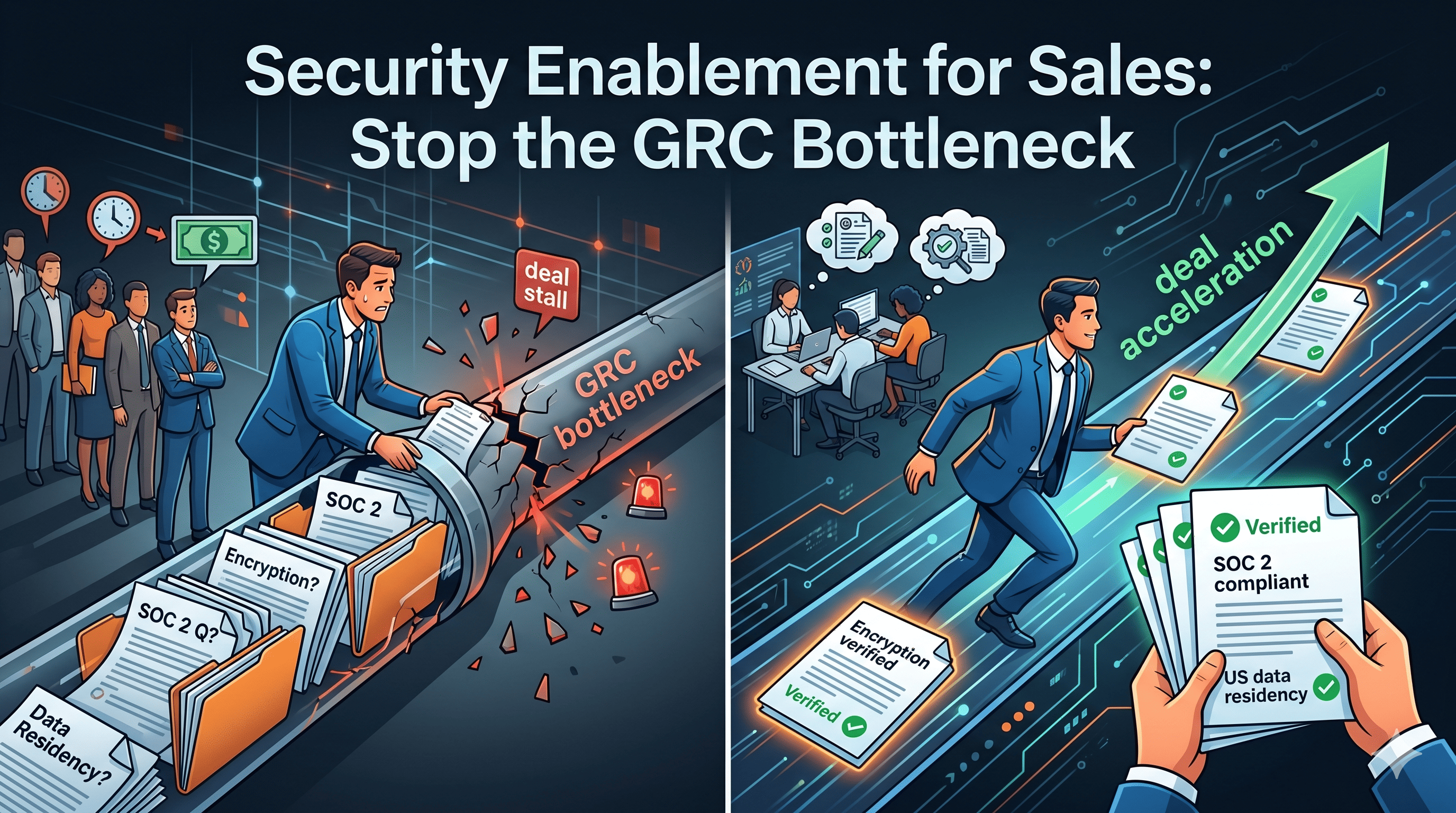
Your team handles dozens of security questionnaires annually. Without proper tools, responding to these becomes a bottleneck. Security questionnaires aren’t going away—they’re becoming more frequent and complex as clients demand proof of your security controls.
The right tools demonstrate your commitment to data protection. They provide documentation that satisfies vendor assessments, regulatory audits, and client security requirements.
Compliance professionals who implement comprehensive security tools reduce questionnaire response time by up to 80 percent while improving accuracy and audit readiness.
Moving Beyond Traditional Point Solutions
Traditional security tools handle individual functions. Firewalls block unwanted traffic. Antivirus software removes malware. But your compliance team needs something different: a way to document, verify, and communicate your entire security posture.
When a potential client asks about your IT security management system, they’re really asking whether you have these tools integrated into a cohesive strategy. They want to know you’re not just deploying isolated solutions—you’re managing security holistically.
The Compliance Connection
Security tools and compliance go hand in hand. Your organization likely manages multiple compliance frameworks: SOC 2, ISO 27001, GDPR, HIPAA, or industry-specific standards. Each requires different controls and documentation.
Modern compliance-focused organizations use tools that bridge the gap between technical implementation and audit evidence. This is where questionnaire automation fits into your broader security tool ecosystem.
Pro tip: Start by auditing which security controls you currently have in place, then map them to your most frequent questionnaire requirements—this reveals which tools would provide the highest ROI for your compliance efforts.
Popular Tool Types and Key Capabilities Compared
Security tools vary dramatically in what they do and how they protect your organization. Understanding which tool serves which purpose helps you build an effective security stack that actually addresses your compliance gaps.
The Major Tool Categories
Organizations typically deploy several distinct tool types, each handling specific security functions:
- Network security tools monitor and control traffic flow, blocking unauthorized access at the perimeter
- Application security testing tools identify vulnerabilities in code before deployment
- Access control systems verify identity and enforce permission policies across systems
- Threat detection and response tools identify suspicious behavior and facilitate incident response
- Compliance and documentation tools capture evidence of your security controls for audits
Static vs. Dynamic Analysis Tools
Application security testing tools fall into two main categories. Static analysis examines code without running it, catching vulnerabilities early in development. Dynamic analysis tests running applications, identifying flaws only visible during execution.
Your development team probably uses both. Static tools catch issues quickly during coding. Dynamic tools validate that fixes actually worked in real environments.
Use this table to compare static and dynamic application security testing approaches:
Federal Security Standards and Tool Selection
Federal cybersecurity frameworks like TIC 3.0 specify which tool capabilities matter most: access control, threat detection, and incident response capabilities. These standards influence how enterprise organizations structure their entire security architecture.
When clients ask about your security posture, they’re often checking whether your tools align with recognized frameworks. This credibility matters for contract negotiations and vendor trust.
Comparing Capabilities That Matter
Not all tools with similar names do the same things. Two firewalls might have vastly different capabilities for logging, threat intelligence integration, or policy management.
When evaluating tools, focus on these differentiators:
- Integration with your existing systems and workflows
- Depth of logging and audit trail capabilities
- Speed of vulnerability detection and remediation
- Ease of generating compliance reports
- Real-time visibility versus batch reporting
The Questionnaire Automation Advantage
Here’s where most organizations miss an opportunity: they buy detection tools but lack systems to document and communicate what those tools are doing. You might have excellent firewalls and intrusion detection, but if you can’t quickly prove it to auditors and clients, the investment doesn’t fully pay off.
Organizations that combine strong detection tools with documented security processes answer questionnaires 80% faster and with significantly higher accuracy.
This is why many teams investigate specific tool comparisons. When comparing different security questionnaire automation solutions, look for platforms that integrate your existing security tools into a unified evidence system.
Pro tip: Map your current tools to your top ten most-asked questionnaire questions first—this reveals which tool capabilities directly impact your compliance burden and where integration with automation tools creates the highest value.
AI Automation in Security Questionnaire Management
Manual questionnaire response is killing your team’s productivity. Your compliance professionals spend weeks on repetitive, time-consuming work instead of strategic risk management. AI automation changes this equation entirely.
The Manual Questionnaire Problem
Consider what happens today: a client sends a 200-question security questionnaire. Your team manually searches through documentation, security tools, and compliance records. Someone writes answers. Someone else reviews them. Inconsistencies emerge. Revisions happen. Days vanish.
Repeat this 10, 15, or 20 times per year across different clients and frameworks. The workload compounds quickly, and your best people get bogged down in administrative tasks.
How AI Automation Addresses This
AI-driven systems fundamentally change the workflow. Instead of manual searching and typing, automation handles the heavy lifting:
- Rapid data collection from your security tools and documentation repositories
- Intelligent matching between your controls and questionnaire requirements
- Consistent answer generation based on your organization's actual practices
- Real-time collaboration so teams can review and refine answers together
- Continuous updates that reflect changes in your security posture
Speed and Accuracy Benefits
AI-powered automation enables rapid collection and verification of security controls data, allowing teams to maintain accurate compliance records efficiently. Organizations using automation typically complete questionnaires in hours instead of weeks.
The accuracy improvement matters equally. When AI extracts answers from your actual security documentation rather than relying on human memory, errors decrease dramatically. This reduces audit findings and client pushback.
Integration With Your Existing Tools
AI questionnaire automation works best when integrated with your existing security infrastructure. Your SIEM, access control system, vulnerability scanner, and compliance platform all contain relevant control evidence.
Automation platforms that connect to these tools automatically populate answers. No manual data entry. No inconsistencies between what your tools show and what you claim in questionnaires.
Building Organizational Trust
When clients see fast, accurate, consistent responses across multiple questionnaires, they develop confidence in your security posture. You’re not scrambling to answer at the last minute—you’re demonstrating organized, controlled processes.
Organizations implementing AI automation for questionnaires reduce response time by 70-80 percent while improving accuracy by 40 percent, strengthening client relationships and competitive positioning.
This matters for sales cycles. POCs complete faster. Contract negotiations move forward without security review delays. Your organization becomes easier to work with.
Pro tip: Start by automating your top five most-requested questionnaires—this proves ROI quickly and builds internal confidence before rolling automation out across your entire compliance program.
Integrating Tools With Compliance Workflows
Owning security tools is one thing. Actually using them to streamline compliance is another. The gap between having tools and integrating them into your workflows is where most organizations lose efficiency and accuracy.
The Integration Challenge
Your organization probably uses 5, 10, or even 15 different security tools. Firewalls log network activity. Access control systems track user permissions. Vulnerability scanners identify weaknesses. Yet your compliance team often bypasses these tools entirely when responding to questionnaires, defaulting to manual documentation searches instead.
This disconnect creates multiple problems: inconsistent answers, missed evidence, wasted time, and increased audit risk.
How Integration Changes Your Workflow
When you embed security tools directly into your compliance process, everything shifts:
- Automated data extraction pulls control evidence from your actual systems
- Real-time verification confirms controls are functioning as documented
- Centralized documentation eliminates searching across multiple platforms
- Continuous monitoring keeps your compliance posture current
- Audit trail creation automatically captures evidence for future reviews
AI-Powered Dashboards for Real-Time Visibility
AI-powered dashboards and automation tools integrate with compliance workflows to enable real-time monitoring and streamlined reporting. This integration improves trust through continuous compliance verification and quick remediation visibility.
Instead of generating quarterly compliance reports, your team gets continuous visibility into whether controls are actually working. When something breaks, you see it immediately and can respond before audit time.
Automating Control Assessment and Documentation
Embedding security tools in compliance workflows enables automated control assessments and continuous monitoring activities as part of your regulatory framework. This approach reduces administrative burden while enhancing compliance quality.
Your team stops manually documenting what systems are doing. Instead, systems document themselves through integrated platforms. This means less paperwork and fewer opportunities for error.
Breaking Down Tool Silos
Integration requires mapping which tools contain which control evidence. Your SIEM has network access controls. Your identity platform tracks authentication. Your patch management system documents vulnerability remediation. Your data encryption tools verify confidentiality controls.
When questionnaires ask about these controls, your automation platform searches the relevant tools and compiles answers automatically.
Organizations integrating security tools into compliance workflows reduce questionnaire completion time by 75 percent while improving accuracy and eliminating manual documentation inconsistencies.
Making Integration Practical
Start with your highest-impact tools and most-asked questions. If 80 percent of your questionnaires ask about access controls, integrate your identity platform first. Once that works, expand to other tools and question types.

Pro tip: Map your three most critical security tools to your top five questionnaire requirements first, then test integration with a single questionnaire before rolling out enterprise-wide.
Mitigating Risks and Avoiding Common Pitfalls
Implementing security tools without a risk management strategy is like building a fortress with no gates. You have defenses, but you haven’t thought about what actually matters. Most organizations stumble on the same preventable mistakes when deploying information security tools.
The Over-Tool Trap
Many organizations buy too many specialized tools without integration strategy. You end up with firewalls, vulnerability scanners, identity platforms, encryption tools, and monitoring solutions all operating independently. Each tool generates its own reports, logs, and compliance evidence.
Your compliance team now manages 10 different logins, 10 different data formats, and 10 different documentation systems. This creates gaps, inconsistencies, and audit failures.
Skipping the Implementation Plan
Companies often deploy tools reactively. A breach happens. An audit fails. A client demands proof of security. Only then do you buy a tool and rush implementation without planning.
Proper implementation takes time. You need to map which tools address which risks. You need to integrate them with your workflows. You need to train your team. Skipping this creates tool graveyards where expensive solutions collect dust.
Common Risk Pitfalls to Avoid
- Incomplete vendor vetting exposes you to tools with poor support or security flaws
- Missing integration planning leaves tool capabilities unused and workflows unchanged
- Inadequate team training means your security controls exist only on paper
- Insufficient documentation creates evidence gaps during audits
- Neglecting continuous updates leaves vulnerabilities unpatched in your tools themselves
Vendor and Integration Risk Management
When selecting security tools, effective vendor risk assessment prevents disasters later. Evaluate not just the tool’s capabilities, but the vendor’s security posture, support structure, and financial stability.
Ask hard questions: Does the vendor undergo regular audits? What’s their incident response time? Do they maintain security certifications? Will they support your compliance frameworks?
The Documentation Deficiency
Your tools generate logs and reports. But questionnaires ask specific questions. Without clear mapping between tool capabilities and compliance requirements, you can’t answer quickly or consistently.
Create documentation that links each security control to the tool that enforces it. This becomes your audit evidence library. When questions arrive, you have answers ready.
Organizations that plan tool implementation with clear risk mitigation strategies experience 60 percent fewer audit findings and 40 percent faster questionnaire completion than those deploying tools reactively.
Continuous Monitoring and Updates
Second-order risks emerge after implementation. Your tools themselves need patching, updating, and monitoring. A vulnerability in your firewall is as dangerous as no firewall at all.
Establish maintenance schedules. Monitor vendor security advisories. Apply patches promptly. This is unglamorous work that prevents catastrophic failures.
Pro tip: Before deploying any new security tool, create a one-page risk mitigation matrix showing which tool addresses which risks, how it integrates with existing systems, and who owns ongoing maintenance—this prevents tool sprawl and ensures every investment delivers measurable value.
Accelerate Your Security Questionnaire Process with AI Automation
Handling complex information security tools and their controls is challenging enough without the extra burden of managing endless security questionnaires. This article highlights how many organizations struggle with slow, manual responses that drain time and risk accuracy. Skypher understands these pain points and transforms your compliance workflow with its AI Questionnaire Automation Tool, turning weeks of work into mere minutes.
Experience fast, precise, and seamless integration with your existing security infrastructure including over 30 API connectors to popular platforms like ServiceNow and OneTrust. Skypher’s solution supports collaboration, real-time updates, and customizable Trust Centers so your team can confidently demonstrate compliance while reducing response times by up to 80 percent. Take control of your questionnaire demands today by visiting Skypher’s homepage and explore how automated workflows improve accuracy and speed. Unlock your organization’s potential by starting with our AI Questionnaire Automation Tool and ensure you never miss deadlines or fall short on trust again.
Frequently Asked Questions
What are information security tools?
Information security tools are technology solutions designed to protect data from unauthorized access, disclosure, disruption, or destruction. They enforce security policies and ensure compliance with regulatory requirements.
Why are information security tools important for compliance?
Information security tools are essential for compliance as they help organizations manage multiple compliance frameworks, such as SOC 2 and GDPR. They demonstrate a commitment to data protection, thereby facilitating smoother vendor assessments and audits.
How do detection and prevention systems work?
Detection and prevention systems work by identifying threats before they can reach critical systems. They serve as an early warning mechanism, enabling organizations to take action before a potential breach occurs.
What is the role of AI automation in security questionnaire management?
AI automation streamlines the questionnaire response process by rapidly collecting data from security tools and documentation repositories, generating consistent answers, and reducing response time significantly, enabling teams to focus on strategic risk management.
Recommended
- IT Security Management System: Enhancing Trust and Efficiency
- Automated Compliance: Transforming Security Reviews
- Complete Guide to Software Compliance Software
- Compliance Risk Meaning: Impact on Security Reviews
- International Trade Compliance – Safeguarding U.S. E-Commerce - ORNER
- Website Security and Data Protection Services | Brainiac Media
- Website Security Essentials: Protecting Small Businesses | Ibrandmedia




.png)